
‘Hacking’ is a relatively new concept in fiction. It’s leapt from the realms of pure science fiction into everyday reality. This means understanding ‘hacking’ can be helpful in any number of genres from suspense/thriller to YA to general fiction.
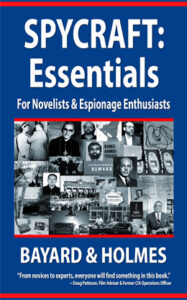
Today is the final guest post from Piper Bayard of the dynamic writing duo, Bayard & Holmes. I really hope y’all pick up copies of their books. I’ve read all of them, even wrote the foreword in one.
I’ve added their books as staples in my reference library and strongly recommend y’all do the same (especially since one is on SALE).
Hackers! Take It Away, Piper!
Most people think of computer invasions when they think of hacking, but any electronic item that transmits a signal can be intercepted and/or hacked.
That means cybersecurity is an issue for every one of us; therefore, unless we are writing historical fiction or some other genre that predates electronics, cybersecurity can a potential issue for any of our characters.
Volumes can be written regarding cybersecurity issues. Rather than offer a comprehensive treatise on the subject—which would no doubt be obsolete before dinner time—today, we’ll focus on common objects in the modern world that can be hacked to spice up our story lines.
Thriller is the genre most likely to involve ‘hackers.’

So we’ll cut to the chase, so to speak, and look at the big picture first. If our character is using electronics to find someone, that character’s capabilities will depend on their nationality and the power of their government or underworld contacts to assist them.
Every allies from folks at the NSA to Anonymous to private security companies could be at their disposal. There are far too many variations to address in a single article, or even a treatise. Suffice to say more than one government has the capability of scooping up every electronic transmission in a given area.
More than one hacker can access everything from a home router to the Pentagon.
As Much or as Little as Necessary

With the vast array of capabilities, this means when, in a crunch, allies can either assist OR should you need a complication, be UNABLE to come to the character’s aid.
Bad guys can apply countermeasures.
Say we flip the coin and our character wants to try to HIDE from government surveillance on the part of any country in the West, Russia, or China.
A character’s best bet is to hide in plain site with a new identity. If that isn’t possible, they must go to an all-cash existence, never carry any electronics of any kind on their person, and avoid all cameras in businesses and on streets.
Since this is pretty close to impossible in First World countries at this point, it’s also best if the character stays on the move in Third World countries. However, human intelligence will still be a threat, and odds are better than good they will be found eventually.
What about a smaller/more intimate picture?

Most of us can look around our workspace and find items that can be hacked. Computers and phones are the most obvious.
We recommend that everyone put a sticky note over their computer camera, because entities from corporations to any number of governments to hackers can and will observe you without it being obvious to you. . . .
We’ll pause a minute for you to cover that camera . . .
Thank you. We feel better talking to you now that strangers can’t see you in your pajamas. If you want to be particularly cautious, cover camera on your phone, as well.
Speaking of cameras . . . Nanny cams, doorbell cameras, security cameras of all kinds, and children’s toys are also regularly hacked by unscrupulous individuals and used by governments foreign and domestic to record information on private citizens.
Why Would Hackers Care About ME?

Most people think, “Why on earth would foreign governments want to digitally molest my nanny cam? I’m just not that interesting.”
Not to promote paranoia, but you actually are that interesting. These are only a few reasons foreign governments want to spy on you:
- To spy on expatriates
- To monitor trends in society
- To improve training of deep-cover operatives
- To better design propaganda efforts in foreign countries
- To gather information on possible targets for covert action
- To identify blackmail targets
- To build files on important foreigners
Yes, foreign governments use Internet devices to collect information on regular citizens to tailor their enormous propaganda efforts, and those data collections on have helped hostile nations level up substantially in their subversion tactics targeted at the West…but that is an article for another day.
Some Folks Just Wanna See the World BURN
We are aware that our computers are open books for governments, both domestic and foreign, as well as hackers.
A hacker can get into a computer and do anything that the computer’s owner can do. They can destroy everything on the device, pilfer through everything on the device, or plant spyware that will record every keystroke.
Computers are most vulnerable when connected to unsecured Internet networks, such as at coffee shops or in hotels, and hackers know this.
Great material for plot lines, right?
There are numerous companies that sell cybersecurity programs to help detect and protect from such attacks. Also, if a computer is turned off, it is safe from hacking.
Hackers and CELL PHONES

Phones are also common targets of governments, local police departments, and hackers.
For example, everyone in the DC area can assume that all of their phone calls are being intercepted by the Russians and the Chinese. That’s true of several large cities in the US and Europe.
In addition to stationary devices, foreign agents, DHS (Department of Homeland Security), and local police departments literally drive around the city with “cell site simulators,” or “Stingrays” in their vehicles that simulate cell phone towers and intercept phone signals.
What’s a Character to Do?

There are two easy ways a character can protect the information on their phone. First, they can put their phone in a faraday bag, which is a bag made of a shielding material that blocks transmissions.
Another way is cheaper and faster than shopping—tin foil. Yes. There is something to the tin foil hat, or in this case, tin foil envelope.
To protect a phone, a character needs three layers of tin foil.
The first layer is smooth. They must be careful to wrap the phone thoroughly, leaving no open seams.
The second layer is crumpled. They crunch up the tin foil, unfold it enough to make it useful, and wrap it around the phone. Again, the character needs to pay attention to seams.
‘The third layer is another smooth layer over the crunched layer. Once the phone is wrapped, anything a hacker could get off of it would be so distorted that it would render the information useless.
This tin foil trick works for computers and key fobs, as well.
Yes, key fobs.
Vehicles with keyless ignition systems, such as pretty much all rental cars these days, can be hacked from outside a building. This is called a “relay attack,” and it can be accomplished with cheap equipment found online or at an electronics store.
One character holds a key fob relay box close to the outside of a building. The box picks up the signal from an unprotected key fob inside and relays it to a second device that a second character holds near the car.
This fools the car, and the vehicle can be unlocked and/or started. Great for car theft, planting surveillance devices, or hiding in a back seat or trunk.
Deliciously creepy, right?
If written well, though, this hack could be used in a romance, and a lover could leave a gift on their beloved’s dashboard. Or perhaps a comedic situation could arise where a character stashed something in a rental car, and they need to get it back on the sly.
Alexa is Listening
Another source for plots comes from voice-controlled speakers such as Alexa or a Smart TV.
Yes. Numerous governments and corporations really are collecting everything said within range of these devices.
Hackers can do the same.
Everything said within range of these devices is collected and transmitted to servers to be analyzed for “search words.” Sorry. This article is too short to discuss what can happen to all of the conversations collected that do not include “search words.”
However, such devices sometimes make mistakes. Voice-controlled speakers have been known to transmit conversations to random individuals on a contact list. For example, a couple can be having a conversation in range of their Alexa or Alexa-equivalent, and it can accidentally be transmitted to some random individual on their contact list.
Cross my heart and hope to die, this has actually happened in real life. The possibilities in fiction are endless!
A more personal digital violation is becoming more common all the time. We’ll be as delicate as possible when describing this . . .
Adults ONLY
Talk about violating privacy For REAL. There is a method of surveillance is called “screwdriving.”
When couples fall in love and become intimate, or they just want a hook up or whatever, sometimes they like to involve certain electronic implements . . . Oh, never mind. Sex toys. We’re talking about sex toys.
Sex toys often now connect to the Internet. The Internet connection allows couples to express their passions, even when they are at a distance, whether across town or across the planet.
Screwdriving is when hackers drive around and seek out these devices in the buildings around them. Hackers then hack the devices in the hopes of delivering a tingly surprise—a digital threesome of sorts.
The romantic and comedic possibilities are endless! Of course so are future episodes of Dateline.
These are only a few of the devices hackers target in real life and in fiction. Others are pacemakers, cars, fitbits, and any other electronic device that connects to the Internet or emits an electronic signal.
Apply imagination, and any of these can be a source of comedy, romance, crime, thrills..or plain terror.
Kind of like this blog.
Apologies.
Thanks for having me!
Wow…Um, Thanks Piper

So thank you, Piper, for this informative and utterly terrifying post.
In all transparency, Piper and I have been friends for almost 12 years. We bond over our healthy dose of paranoia and the NSA LOVES when we chat on the phone.
When the Alexas first came out, my brother bought everyone in the family Alexas for Christmas. It was an incredibly thoughtful gift…
…that I left in its box (buried in another box).
Then, my mom got Ringr and I had a FIT for a BIT…but can only preach so much.
I have a TON I could add to this post, but we’ll save that for another day since many of you might already be hiding in a three-layered tent made from emergency shock blankets (foil) eating cookie dough.
For now, The Edge: How to Write Mystery, Suspense & Thriller is available ON DEMAND (sign up HERE and use Thrill10 for $10 off). The recording turned out FANTASTIC, so check it out. This class pairs really well with everything Piper has talked about the past four posts.
I will be uploading more classes this week, and Piper will soon be teaching as well for Bad Lamb Academy. YAY!
We LOVE hearing From You!
Have you used hacking in one of your plots? What genre was it?
If y’all have any questions for Piper, this is the time. She’s here and available from her underground silo 😛 .
 SALE!
SALE!
FINAL DAYS ONLY $2.99 — Click Here
What do the main intelligence agencies do and where do they operate? How do they recruit personnel? What are real life honey pots and sleeper agents? What about truth serums and enhanced interrogations? And what are the most common foibles of popular spy fiction?
With the voice of over forty years of experience in the Intelligence Community, Bayard & Holmes answer these questions and share information on espionage history, firearms of spycraft, tradecraft techniques, and the personalities and personal challenges of the men and women behind the myths.
Though crafted with advice and specific tips for writers, SPYCRAFT: Essentials is for anyone who wants to learn more about the inner workings of the Shadow World.
“For any author, this is the new bible for crafting stories of espionage.”
~ James Rollins, New York Times Bestselling Author of The Demon Crown

Piper Bayard and Jay Holmes of Bayard & Holmes are the authors of espionage tomes and international spy thrillers. Please visit Piper and Jay at their site, BayardandHolmes.com. For notices of their upcoming releases, subscribe to the Bayard & Holmes Covert Briefing. You can also contact Bayard & Holmes at their Contact page, on Twitter at @piperbayard, on Facebook at Piper Bayard, or at their email, BayardandHolmes@protonmail.com.







7 comments
1 ping
Skip to comment form
Great post, and yes, I use hacking with my protagonist, Camilla Lee, an MI6 agent. MI6 hack the phones of those they are investigating and are able to look and listen-in 24/7. Probably bullshit, but I make it work.
Glad you liked the post. Thank you. . . . I wish it were bullshit. Government agencies can absolutely do that.
lol – thanks for a brilliant article. Being a wee bit paranoid myself, I knew about some of this stuff – e.g. the Alexa debacle – but I definitely did not know about how keyfobs can be hacked, amongst other goodies. And then there’s social media…-facepalm-
We all have the right to choose the degree of risk we’re prepared to take, but most people on or connected to the internet haven’t got a clue about the risks they take every day. To me that’s just ‘head-in-the-sand’ thinking. 🙁
I use a spoofer (an electronic device that can read and recreate radio signals) in the later books in my Sara X series. In book three of the series she uses it to unlock the back hatch of a food delivery truck while a colleague distracts the driver. In book four she uses it to copy the signals from the smartphone of the district attorney to gain entry to his smarthouse.
Stephen King used key fob hacking by the bad guy in Mr. Mercedes. The results were bad (as they so often are in Mr. King’s work).
I also suggest leaving credit cards, especially those with chips, in a metal box to keep an RFID reader from harvesting fun things like bank accounts and other info.
Yes, I wrote a hacker character into my sci-fi/dystopian novella “The Implant.”
At a pre-pandemic DefCon, one of the panels was dedicated to hacking sex toys. I still laugh every time I think of that. And yes, that *would* create some definite chicanery.
[…] Hacking: The Secret Spice of Modern Storytelling […]